WooCommerce DDoS & Bot Protection Guide: Secure Your Store
DDoS Protection Guide: Securing WooCommerce Stores Against Bot Attacks

Introduction: The Modern E-Commerce Threat Landscape
The intersection of global retail and digital infrastructure has created a complex environment where e-commerce platforms are continually subjected to increasingly sophisticated cyber threats. The transition from simplistic, volumetric network-layer attacks to complex, application-layer (Layer 7) distributed denial of service (DDoS) and bot-driven campaigns has fundamentally altered the security requirements for online retail architectures. Industry data indicates a staggering 417% increase in the volume of Layer 7 DDoS attacks within the retail sector between the latter half of 2022 and the first half of 2023, with regions such as the United States, Australia, Germany, and France experiencing the highest incidence rates. Automated attacks targeting application business logic have definitively emerged as the leading threat for online retailers worldwide.
WooCommerce, operating as an extensive e-commerce plugin atop the WordPress Content Management System (CMS), currently powers a vast percentage of global e-commerce. Its open-source nature, while highly extensible and beneficial for custom development, inadvertently exposes a predictable architectural footprint to malicious threat actors. Built upon an intricate network of API connections, third-party dependencies, and dynamic PHP rendering, WooCommerce installations are particularly vulnerable to business logic abuse, client-side attacks, and rapid resource exhaustion. Security incidents, which persistently threaten operational stability throughout the calendar year, reliably spike during high-volume periods such as holiday shopping seasons, flash sales events, and highly anticipated product launches.
A successful security incident on a WooCommerce platform yields severe secondary consequences beyond the immediate technological failure. These include elevated infrastructure and scaling costs, degraded service latency for legitimate consumers, permanent reputational damage, and ultimately, severe customer churn. The contemporary breed of automated bot is capable of executing nuanced operations that mimic human behavior, rendering legacy security measures—such as basic IP blocking and static signature analysis—largely obsolete. Malicious bot activity on WooCommerce sites is projected to rise sharply, potentially accounting for 68% of all traffic interactions by 2025. To maintain resilience, a multi-layered, defense-in-depth architecture must be deployed, seamlessly integrating edge-network mitigation, server-level traffic shaping, and application-layer behavioral analysis.
The Anatomy of Bot-Driven Threats in E-Commerce
Bots currently account for nearly 50% of all internet traffic, and a significant proportion of this automated traffic is fundamentally malicious. Bot management refers to the strategic implementation of software solutions designed to block undesired or malicious internet bot traffic while simultaneously allowing useful, verified bots (such as search engine crawlers and uptime monitors) to access web properties unobstructed. A robust bot management architecture must distinguish between human visitors and automated scripts, evaluate IP reputation, challenge suspicious entities via non-intrusive tests, and rate-limit aggressive resource consumption.
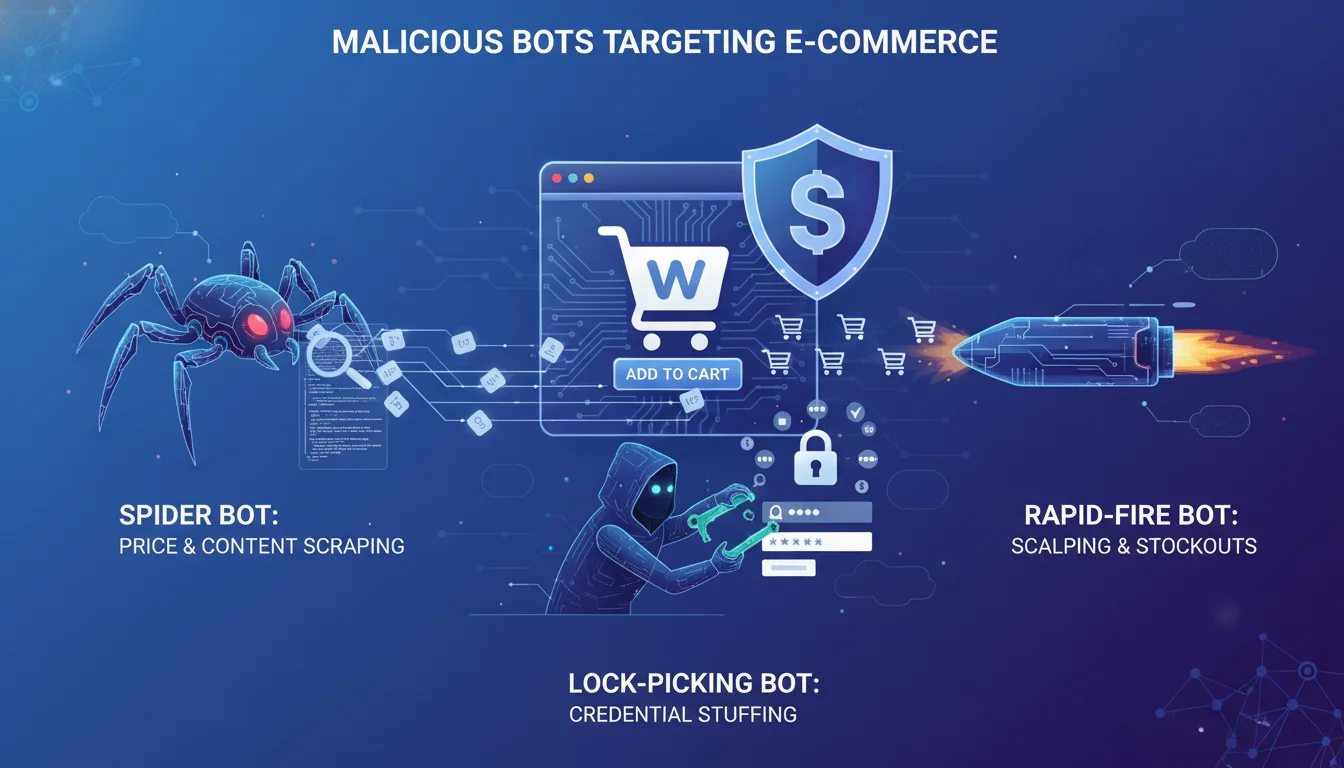
Within the WooCommerce ecosystem, automated threats manifest across several distinct operational categories:
- Reconnaissance and Scraping Bots: These bots meticulously crawl e-commerce sites to extract pricing data, monitor availability, and harvest product metadata. Powered by modern artificial intelligence, these scraping tools provide competitive intelligence to rivals, or harvest assets to construct sophisticated phishing sites and fake marketplaces. They also scan for unreleased items or hidden sales endpoints, leading to unexpected traffic spikes and inflated bounce rates when non-existent pages are queried.
- Scalping and Sneaker Bots: Designed specifically to target high-demand, limited-edition merchandise, these programs rapidly acquire and hoard valuable inventory the moment a product launches. The objective is to deny legitimate consumers access, allowing the fraudster to resell the hoarded items at a significant premium on secondary markets.
- Credential Stuffing Bots: Taking advantage of seasonal traffic spikes, these bots launch automated account takeover (ATO) attacks against the WooCommerce /wp-login.php or “My Account” pages. They utilize massive databases of stolen credentials to breach user accounts, subsequently exposing personal data and stored payment information.
- Fake Account Creators and Promo Abusers: These automated scripts utilize temporary email addresses to rapidly generate hundreds of customer profiles. This facilitates the exploitation of single-use promotional codes, artificially inflates marketing metrics, and severely disrupts the merchant’s bottom line.
- DDoS and Application Stressors: While some bots focus on data extraction or financial fraud, others exist solely to overwhelm the server. By aggressively targeting computationally expensive endpoints, these bots force the database and PHP workers to exhaust their allocated resources, effectively denying service to all users.
Legacy solutions relying solely on IP address blocking are inefficient against modern botnets, which utilize massive residential proxy networks to continuously rotate their origin IP addresses. Therefore, mitigating these threats requires a comprehensive understanding of how specific WooCommerce endpoints are targeted and exploited.
The Mechanics of Layer 7 DDoS and Asymmetric Resource Exhaustion
Unlike traditional Layer 3 or Layer 4 DDoS attacks that seek to saturate raw network bandwidth with UDP or TCP floods, Layer 7 attacks specifically target the application layer (HTTP/HTTPS). These attacks weaponize the asymmetric nature of dynamic web applications. A single, low-bandwidth HTTP GET or POST request generated by a malicious bot requires the origin server to initialize the WordPress core, execute complex PHP logic, query the MySQL or MariaDB database, and dynamically render a payload. By dispatching a relatively small, coordinated burst of requests to computationally expensive endpoints, an attacker can rapidly exhaust the server’s FastCGI Process Manager (PHP-FPM) worker pool and database connection limits.
The XML-RPC Protocol Vulnerability
One of the most persistent vectors for automated attacks—including massive DDoS and relentless brute-force attempts—is the legacy XML-RPC feature (xmlrpc.php). Originally introduced to allow data transmission via HTTP for early mobile applications and pingbacks, modern WordPress and WooCommerce installations no longer require its functionality, as it has been entirely superseded by the robust WordPress REST API.
The core vulnerability of XML-RPC lies in its efficiency for attackers. A brute-force script attempting to guess administrative passwords that might normally require 10,000 distinct HTTP requests can accomplish the exact same goal in merely 100 requests by utilizing the system.multicall method within XML-RPC. This multiplier effect creates a severe resource drain, particularly on shared hosting environments or undersized Virtual Private Servers (VPS).
Because attack prevention must ultimately happen at the server level, merely ignoring XML-RPC traffic at the edge is often insufficient. Administrators must disable XML-RPC functionality directly via server directives. This can be achieved using Apache .htaccess rules, NGINX deny blocks, or comprehensive security plugins. Regular audits of server logs for repeated POST requests to /xmlrpc.php, unusually large request payload sizes, or sudden bursts from specific IP subnets are critical for identifying reconnaissance preceding a volumetric attack.
The WooCommerce Cart Fragments Vulnerability (wc-ajax=get_refreshed_fragments)
Within the specific architecture of WooCommerce, one of the most heavily targeted and resource-intensive endpoints is the cart fragmentation script, identifiable in web server access logs by the query string /?wc-ajax=get_refreshed_fragments. This AJAX endpoint was historically designed to seamlessly update the “mini-cart” widget located in the website’s header whenever a user adds or removes a product, without requiring a full browser page reload.
Because this request relies on unique, session-specific user data to dynamically calculate cart totals, local taxes, and shipping estimates, it fundamentally forces the server to bypass standard edge caching mechanisms (such as Cloudflare) and server-side page caching plugins (such as WP Rocket or LiteSpeed Cache). Threat actors exploit this architectural necessity by directing vast botnets to repeatedly issue POST or GET requests to this exact, uncachable URL.
Even a highly modest botnet generating a mere 3 to 5 requests per second to the get_refreshed_fragments endpoint can induce noticeable latency.
When scaled to thousands of requests per minute, the attack easily cripples an inadequately provisioned web server, leading to 502 Bad Gateway or 504 Gateway Timeout errors. In some instances, administrators note that these requests continue even after implementing caching plugins because the endpoint explicitly instructs the server to render dynamic output.
Historically, developers attempted to mitigate this vulnerability by entirely disabling the WooCommerce cart fragments AJAX call via custom PHP functions hooked into wp_enqueue_scripts, effectively dequeuing the wc-cart-fragments script. However, completely disabling this feature degrades the user experience by breaking dynamic cart updates across the storefront. While modern iterations of WooCommerce have transitioned toward utilizing the Store API and WooCommerce Checkout Blocks—which offer more resilient session handling—the legacy AJAX endpoint remains a frequent target on older themes or highly customized storefronts.
Furthermore, some attackers have discovered that when the fragments endpoint is disabled, WooCommerce defaults to standard ?add-to-cart= GET requests, which can be equally manipulated by bots to bypass caching. Consequently, managing this threat requires sophisticated NGINX or Apache traffic shaping rather than simply disabling core application features.
Admin-Ajax and REST API Exploitation
Beyond cart fragments, automated attacks frequently target the core WordPress execution pathways, specifically /wp-admin/admin-ajax.php and the WordPress REST API (/wp-json/). The admin-ajax.php file was originally introduced to handle administrative background tasks and frontend asynchronous requests, such as complex product filtering algorithms or infinite scrolling pagination. However, poorly optimized third-party plugins (such as visual page builders or search-and-replace tools) often bombard this endpoint, an issue severely exacerbated by the WordPress Heartbeat API, causing sustained, heavy CPU utilization.
Similarly, REST API violations occur when API endpoints are utilized in unintended ways. Because retail sites handle immense traffic volumes, manage proprietary data, and heavily integrate with third-party fulfillment and marketing applications through APIs, these endpoints are immensely attractive to cybercriminals. Malicious actors exploit the REST API to execute data scraping, deploy account takeover attacks, and automate inventory enumeration. The sheer volume of modern API calls—with enterprise solutions like Cequence Security analyzing over 10 billion API calls daily for anomalies—underscores the critical necessity of API-specific rate limiting and behavioral filtering.
Business Logic Abuse: Denial of Inventory and Hoarding
Business logic attacks differ fundamentally from traditional hacking. Instead of exploiting technical software vulnerabilities (like SQL injection or Cross-Site Scripting), they exploit the intended functionality and standard operational processes of an application. In the retail sector, attackers leverage business logic to manipulate dynamic pricing models, bypass purchasing limits, or execute massive inventory hoarding operations. Security analytics reveal that business logic attacks constitute approximately 42.6% of all attacks directed at retail websites, representing a significant year-over-year escalation.
The Mechanics of Denial of Inventory (Hoarding)
Denial of inventory, frequently referred to as inventory hoarding, is a specialized cybersecurity attack wherein an automated script or “shopping bot” repeatedly adds limited-availability e-commerce products into a shopping cart without ever completing the final financial transaction. The objective is to manipulate the WooCommerce inventory management engine into categorizing the targeted product as “out of stock” or temporarily unavailable.
When legitimate human consumers navigate to the affected product page, they are presented with an out-of-stock notification, entirely preventing successful conversions. This attack vector inflicts dual damage upon the merchant: immediate, direct revenue loss due to abandoned legitimate sales, and long-term brand degradation as frustrated consumers permanently migrate to competitor storefronts.
The motivations driving denial of inventory attacks are diverse:
- Scalping and Profiteering: Fraudsters deploy sophisticated sneaker bots to rapidly acquire and hoard highly sought-after, limited-edition merchandise. By denying access to the general public, the scalpers artificially inflate demand, ensuring they can eventually secure the inventory and resell it at a massive premium on secondary markets.
- Competitive Sabotage: Competing businesses, or professional threat actors directly hired by them, may deploy hoarding bots to artificially deplete a rival’s inventory during peak sales events (such as Black Friday). This tactic effectively drives consumer traffic back to the attacker’s own platform.
- Application Stress Testing: In some instances, rapid “Add to Cart” operations are utilized as a highly targeted form of application-layer DDoS, designed specifically to stress the database engine as it desperately attempts to calculate complex real-time inventory decrements, apply tax logic, and lock corresponding database rows.
The WooCommerce Draft Order Vulnerability
The architectural handling of checkout sessions within modern WooCommerce installations—specifically those utilizing the newer block-based checkout experience—creates a unique vulnerability to inventory hoarding. When a user or automated bot initiates the checkout process via WooCommerce Blocks, the system automatically generates a “Draft” order in the database.
Crucially, the creation of this draft order places an immediate, temporary hold on the physical stock associated with the items in the cart. By default, WooCommerce enforces a 10-minute reservation on this stock to guarantee availability while the user completes the payment process. If an advanced botnet initiates thousands of concurrent checkout block requests across distributed IP addresses, it rapidly generates thousands of unique draft orders. Because each individual draft order reserves stock for 10 minutes, the entire global inventory of a product can be instantaneously locked, completely paralyzing sales for that specific SKU.
While WooCommerce employs a scheduled background cron job (woocommerce_cleanup_draft_orders) that runs daily to purge abandoned draft orders, this interval is vastly inadequate for mitigating a real-time, high-velocity bot attack. Furthermore, if the global “Hold Stock” timer (configured via WooCommerce > Settings > Products > Inventory) is set to default or inflated values (often 60 minutes or more for pending payments), the inventory denial can persist for extended periods, necessitating immediate manual intervention by database administrators to cancel the pending orders and restore stock levels.
Automated Fake Orders and Card Testing
Closely related to the concept of inventory hoarding is the phenomenon of fake order generation and programmatic card testing. Attackers utilize automated scripts, residential proxy networks, and temporary, disposable email addresses to flood the WooCommerce checkout form. These bots frequently place dozens of sample orders within minutes, utilizing randomized or fabricated customer details.
The primary driver for generating fake orders is card testing (frequently referred to as carding). Cybercriminals acquire vast databases of stolen credit card numbers from illicit dark web marketplaces. Because they do not know which cards remain active or hold a sufficient balance, they deploy bots to rapidly process small transactions on vulnerable WooCommerce checkouts to validate the credentials. To minimize costs, the attackers usually target the lowest-priced items in the store, or exploit “pay-what-you-want” donation products. If the store lacks adequate endpoint protection, the payment gateway processes thousands of fraudulent validation requests in rapid succession.
The operational and financial consequences of card testing are exceptionally severe. Payment processors (such as Stripe, Authorize.net, or PayPal) enforce strict algorithmic risk thresholds. If a WooCommerce merchant submits an excessive volume of declined, fraudulent transactions, the payment processor will issue severe financial penalties, withhold processing funds, or permanently terminate the merchant’s account, paralyzing the business’s ability to operate. Furthermore, the operational burden of manually identifying and refunding successful fraudulent transactions before chargebacks are initiated creates immense administrative overhead.
Edge Network Defense: Enterprise Web Application Firewalls (WAFs) and CDNs
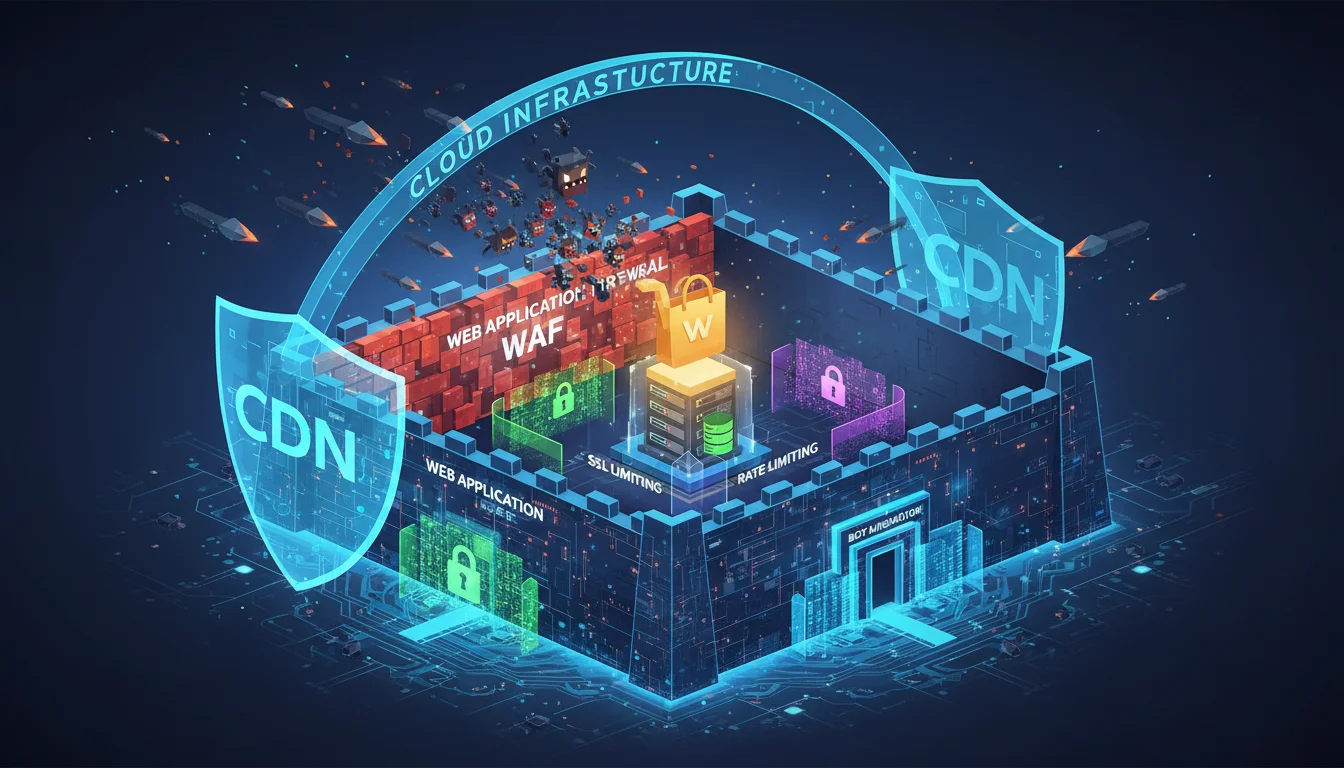
The most effective, resource-efficient strategy for mitigating volumetric and application-layer bot attacks is to neutralize the threat at the network edge, long before the malicious HTTP requests ever reach the origin WordPress server. Content Delivery Networks (CDNs) equipped with robust, dynamically updated Web Application Firewalls (WAFs) act as the primary, indispensable defensive perimeter.
Comparative Analysis of Bot Mitigation and WAF Solutions
The current market for WAF and Bot Management solutions is highly diverse, ranging from all-purpose systems suitable for small-to-medium businesses (SMBs) to highly specialized, AI-driven platforms designed explicitly for massive enterprise retail architectures.
Recent independent benchmarking data from 2024 and 2025 highlights the varying efficacies of these platforms.
| Vendor / Platform | Architectural Focus & Key Strengths | Notable Features & Bot Mitigation Strategies | Performance Metrics (2024-2025 TPR / FPR) |
|---|---|---|---|
| Cloudflare WAF | All-purpose, global Anycast CDN, highly scalable for SMB to Enterprise. | Super Bot Fight Mode, JavaScript Turnstile challenges, advanced Cache Rules, Page Rules, DDoS mitigation. | True Positive Rate (TPR): 69.3% False Positive Rate (FPR): 0.062% |
| F5 BIG-IP Advanced WAF | Enterprise-grade, rapid deployment within cloud environments (AWS/Azure). | Advanced bot signatures, behavioral analysis, highly accurate payload inspection. | TPR: 78.89% FPR: 2.8% Balanced Accuracy: 88.045% |
| DataDome | Enterprise edge-based protection rigorously optimized for e-commerce and APIs. | AI-powered real-time behavioral detection, zero-day threat adaptation, invisible JavaScript challenges. | Not explicitly benched in standard OWASP tests, but leads e-commerce bot management. |
| Prophaze | AI-Native, Kubernetes-integrated autonomous Bot Mitigation. | Behavioral detection analyzing user intent, ultra-low latency within clusters, self-learning algorithms. | Kubernetes-native deployment metrics. |
| Sucuri WAF | Cloud-based firewall strictly focused on WordPress/website security and post-hack remediation. | Virtual patching, brute force protection, unlimited malware removal guarantees. | Highly rated for SMB remediation; lacks enterprise API handling. |
| AWS WAF | Amazon-native infrastructure protection designed for deep integration. | CloudWatch analytics, custom rulesets, managed IP reputation lists (e.g., AWSManagedIPDDoSList). | Baseline OWASP CRS protection. |
| Cequence Security | Unified API/WAF/AI Bot and fraud defense for massive retail enterprises. | Enterprise hybrid deployment, handles over 10B API calls daily, protects against ATO without app code changes. | Enterprise custom scaling. |
While platforms like Sucuri offer excellent malware remediation and virtual patching protocols, performance benchmarks and overall user satisfaction metrics frequently favor Cloudflare for raw edge-caching speed, granular bot control, and ease of deployment. For high-volume e-commerce architectures, specialized AI-driven solutions like DataDome or Prophaze analyze sub-second behavioral biometrics—such as mouse movement anomalies, rapid DOM interactions, and typing cadence—to distinguish between humans and headless browsers, entirely eliminating the reliance on static IP blocklists which are easily circumvented.
Cloudflare Architecture for WooCommerce Security
Implementing Cloudflare for a WooCommerce installation requires precise, nuanced configuration. The objective is to balance aggressive content caching for optimal performance with strict security rules to prevent malicious bot intrusion, without inadvertently caching dynamic shopping cart data.
1. Transitioning to Cache Rules and Configuration Rules
Historically, Cloudflare relied heavily on “Page Rules” to govern URL-specific behavior. However, with the deprecation of Page Rules in favor of the more robust Cache Rules and Configuration Rules engines (a transition fully executing between 2024 and 2025), administrators must adapt to the modern ruleset logic. To prevent Cloudflare from serving cached, stale data to dynamic e-commerce functions, strict bypass rules must be implemented.
A definitive “Bypass Cache” directive must be explicitly applied to the following URI paths:
- /wp-admin/*: Essential for protecting the administrative dashboard, bypassing cache, disabling performance apps (like Rocket Loader) that interfere with backend logic, and elevating the Security Level to “High”.
- /checkout/_ and /cart/_: Critical for ensuring that session-specific transactional data, shipping estimates, and payment gateways operate dynamically without serving cached user data.
- ?wc-ajax=: Specifically targeted to prevent the caching of the cart fragmentation script, ensuring real-time inventory and cart updates.
- /preview/_ and /ajax/_: Ensures content editors and dynamic frontend widgets always receive fresh server responses.
Conversely, enabling Automatic Platform Optimization (APO) or strict edge caching for static assets significantly reduces the Time to First Byte (TTFB) for global users. This allows the origin WordPress server to reserve its crucial CPU cycles strictly for handling uncached REST API and checkout requests. Standard security protocols such as SSL/TLS Full (Strict), Always Use HTTPS, HSTS, TLS 1.3, and Brotli compression should be universally enabled. Furthermore, managed rulesets must ensure protections against widespread vulnerabilities like Log4J injections, Shellshock, and common OWASP WordPress exploits.
2. Custom WAF Expressions and Heuristic Bot Management
Cloudflare’s Custom Rules engine allows administrators to craft highly specific, boolean logical expressions to block, challenge, or rate-limit traffic before it successfully engages the WooCommerce checkout. By intelligently combining URI path targeting with Cloudflare’s proprietary Bot Management scoring system, highly effective barriers can be erected against card testing and inventory hoarding.
A bot score within Cloudflare ranges from 1 to 99. A score below 30 strongly indicates that the request originates from an automated script, API service, or headless browser. A high score indicates a human operating a standard desktop or mobile web browser. To protect the checkout without introducing friction for legitimate human buyers, an administrator can deploy the following WAF expression:
(http.request.uri.path contains "/checkout") and (http.request.method eq "POST") and (cf.bot_management.score lt 30) and not (cf.bot_management.verified_bot)
When a request matches this specific expression, the WAF executes a “Managed Challenge” or “Block” action. This ensures that only highly suspicious traffic attempting to submit data via POST to the checkout endpoint is intercepted. Verified bots (such as Googlebot, Bingbot, or legitimate payment gateway webhooks from Stripe or PayPal) are explicitly evaluated and allowed to bypass the restriction to prevent operational interference.
3. Interactive Challenges, Cookies, and Cloudflare Turnstile
Legacy CAPTCHA systems (such as Google reCAPTCHA v2) impose significant user friction, negatively impacting conversion rates and creating accessibility barriers. Furthermore, legacy CAPTCHAs are routinely bypassed by human-powered “CAPTCHA farms” operating in low-wage economies, rendering them increasingly ineffective against determined attackers.
Cloudflare Turnstile serves as a modern, privacy-focused, non-interactive alternative. It utilizes sophisticated JavaScript execution challenges, cryptographic proof-of-work algorithms, and browser telemetry to validate human presence without requiring the user to solve visual puzzles. Integrating Turnstile directly into the WooCommerce checkout flow (via dedicated WordPress plugins) ensures that the final POST payload required to generate a WooCommerce order is structurally impossible to execute via a simple Python script or headless botnet that lacks a complete JavaScript execution environment.
For advanced persistent threats, administrators can deploy custom WAF rules that mandate the presence of specific session cookies. By issuing a cryptographic cookie when a user legitimately interacts with the site’s frontend, the WAF can automatically block any direct POST requests to the checkout endpoint that lack this cookie, effectively neutralizing bots that attempt to bypass the storefront and hit the API directly.
Server-Level Traffic Shaping and Rate Limiting
If malicious traffic successfully bypasses the edge network—whether due to WAF misconfiguration, sophisticated proxy rotation, or attackers discovering the origin server’s direct IP address—the web server itself must be equipped to rigorously shape and restrict incoming traffic.
NGINX Rate Limiting: The Leaky Bucket Algorithm
For high-performance WooCommerce installations, NGINX is the industry standard web server. NGINX utilizes the “leaky bucket” algorithm to process and enforce rate limiting. This architecture fundamentally acts as a first-in-first-out (FIFO) queue. If the rate of incoming HTTP requests exceeds a predefined processing threshold, the “bucket” overflows, and NGINX immediately drops the excess requests, returning a customizable HTTP status code (typically 429 Too Many Requests or 503 Service Unavailable).
Implementing effective NGINX rate limiting requires the configuration of two distinct directives. First, the limit_req_zone is defined within the global http context of the nginx.conf file. This establishes the shared memory zone required to continuously track client IP addresses and calculate their request frequencies.
http {
limit_req_zone $binary_remote_addr zone=woo_checkout:10m rate=5r/m;
limit_req_zone $binary_remote_addr zone=api_limit:10m rate=10r/s;
limit_req_status 429;
}
In this configuration, the $binary_remote_addr variable utilizes a highly compressed, 64-byte binary representation of the client’s IP address.
This compression allows a 10-megabyte memory zone (10m) to track the state of approximately 160,000 discrete IP addresses simultaneously. The rate for the woo_checkout zone is strictly limited to 5 requests per minute (5r/m), while the api_limit zone allows a more permissive 10 requests per second (10r/s).
The second critical step involves applying these zones to specific vulnerable WooCommerce and WordPress locations using the limit_req directive.
Nginx
server {
# Protect the WordPress Login
location = /wp-login.php {
limit_req zone=woo_checkout burst=2 nodelay;
# FastCGI processing directives follow...
}
# Protect the Admin-Ajax Endpoint
location ~* \/wp-admin\/admin-ajax\.php$ {
limit_req zone=api_limit burst=20 nodelay;
# FastCGI processing directives follow...
}
# Protect the REST API
location /wp-json/ {
limit_req zone=api_limit burst=20 nodelay;
}
}
The incorporation of the burst and nodelay parameters is critical for maintaining complex application functionality without dropping legitimate user interactions. Without a burst parameter, NGINX strictly enforces exact, millisecond-level spacing between requests. If a rate is set to 1 request per second, and a user makes two legitimate, asynchronous AJAX requests within 100 milliseconds, the second request is instantly rejected. Adding burst=20 allows the leaky bucket to accommodate a rapid succession of 20 concurrent requests, queuing them. Adding the nodelay flag ensures that these burst requests are processed instantly by the upstream PHP worker pool, rather than being artificially delayed to perfectly match the specified mathematical rate limit.
This sophisticated configuration is absolutely essential for protecting /wp-login.php from massive credential stuffing campaigns, and /wp-admin/admin-ajax.php from total resource exhaustion. By rate-limiting admin-ajax.php, administrators prevent bots from overwhelming the server, while still permitting legitimate frontend background tasks (like infinite scroll or dynamic filtering) to execute within the defined burst thresholds. Furthermore, administrators can implement complex whitelisting rules within NGINX to ensure trusted IP addresses completely bypass rate limitations.
Apache .htaccess Directives and Mod_Evasive
For environments utilizing the Apache HTTP Server, the .htaccess configuration file provides powerful, directory-level mechanisms for neutralizing automated threats. While Apache is generally less performant than NGINX under heavy load due to its process-driven architecture, it can effectively block known bad actors before they execute expensive PHP scripts.
Administrators can utilize the mod_setenvif module to rigorously evaluate the User-Agent headers supplied by incoming requests. Many rudimentary bots and scrapers utilize default, identifiable user agents (such as specific Python request libraries or generic crawling definitions) that can be easily identified and unconditionally denied access.
Apache
<IfModule mod_setenvif.c>
SetEnvIfNoCase User-Agent ".*gptbot.*" bad_bot
SetEnvIfNoCase User-Agent ".*Go-http-client.*" bad_bot
SetEnvIfNoCase User-Agent ".*python-requests.*" bad_bot
Order Allow,Deny
Allow from All
Deny from env=bad_bot
</IfModule>
While user agents are easily spoofed by advanced, determined attackers, implementing this baseline hygiene eliminates vast swaths of unsophisticated scraping, reconnaissance bots, and automated spam engines. Furthermore, administrators can invoke mod_ratelimit or install dedicated third-party modules like mod_evasive to implement robust, server-level DDoS prevention and brute-force protection tailored explicitly to the wp-login.php pathway. mod_evasive detects possible attack patterns on the network and integrates with system tools like iptables to drop connections at the firewall level when anomaly thresholds are breached.
Application-Layer Defenses: WooCommerce Core and API Enhancements
Relying exclusively on edge networks and server traffic shaping is insufficient; the e-commerce application itself must be hardened to recognize, validate, and natively mitigate business logic abuse.
WooCommerce 9.x Built-In Mitigation and Rate Limiting
Recognizing the escalating severity of card testing, API abuse, and inventory hoarding, the WooCommerce core engineering team has introduced highly sophisticated rate-limiting features natively into the Store API and Checkout Blocks architecture, beginning with version 8.9 and fully maturing in the WooCommerce 9.x branch.
These built-in protections specifically restrict the velocity of requests directed at the highly vulnerable /checkout, /cart, and /product endpoints. By navigating to WooCommerce > Settings > Advanced > Features and enabling the “Rate limiting Checkout block and Store API” toggle, administrators enforce a strict, application-level threshold: a maximum of 3 POST checkout requests per 60 seconds.
Crucially, the release of WooCommerce 9.8 expanded this capability significantly to include batch processing for all Store API endpoints and introduced the highly adaptable woocommerce_store_api_rate_limit_id filter. Previously, the built-in rate limiting relied exclusively on evaluating the client IP address. However, sophisticated botnets easily bypass IP-based limits by rotating through millions of residential proxy IPs. The new filter allows developers to inject advanced custom fingerprinting logic—combining the IP address with Accept-Language headers, specific user-agent hashes, or proprietary session tokens—to track and throttle aggressive clients regardless of their IP rotation frequency.
Mitigating Draft Order Inventory Hoarding and Session Modification
To permanently resolve the denial of inventory attacks caused by the 10-minute draft order hold, administrators must implement precise application-level modifications. The simplest initial approach involves utilizing the standard WooCommerce inventory settings to drastically reduce the global “Hold Stock” timer to the lowest acceptable operational threshold (e.g., 5 to 10 minutes).
However, relying solely on the native WordPress cron system (woocommerce_cleanup_draft_orders) to clear these draft orders is often too slow during an active, volumetric attack. Advanced mitigation requires custom PHP snippets or specialized plugins (such as “Auto-Close Old Pending Orders”) to aggressively identify unauthenticated draft orders and release the associated inventory holds instantly upon timeout.
Furthermore, developers can manipulate the underlying session lengths. By default, a WooCommerce cart session lasts for 48 hours. While this is designed for customer convenience, it can be exploited. Utilizing the wc_session_expiring and session_expiration hooks, developers can drastically shorten this window, preventing bots from maintaining massive, prolonged session states across the database.
PHP
// Custom Snippet to modify session expiration
add_filter( 'wc_session_expiring', function( $seconds ) {
return 60 * 60 * 11; // 11 hours
} );
add_filter( 'wc_session_expiration', function( $seconds ) {
return 60 * 60 * 12; // 12 hours
} );
The Role of WordPress Security Suites and Anti-Fraud Tools
Integrating a comprehensive, enterprise-grade WordPress security plugin provides a unified dashboard for endpoint firewall management, malware signature scanning, IP reputation filtering, and vulnerability detection.
| Security Suite | Primary Mitigation Strengths | Firewall Architecture | Vulnerability/Malware Handling |
|---|---|---|---|
| Wordfence Security | Market-leading threat intelligence, strict 2FA enforcement, live traffic monitoring, brute-force limits. | PHP-based Endpoint Firewall (executes prior to WP core loading). | Global malware signature database, 24-hour incident response for premium tiers. |
| Sucuri Security | Global performance optimization via CDN, dedicated focus on post-hack cleanup and incident response. | Cloud-based WAF (requires complete DNS routing). | Advanced server-side scanning, continuous monitoring. |
| MalCare | Exceptionally low server resource overhead, one-click automated malware removal. | Cloud-based firewall executing off-server to preserve CPU. | Deep cloud scanning, exceptional post-compromise recovery efficiency. |
| Shield Security | Strict automated bot blocking, AI-driven traffic scanning, absolute prevention of core file tampering. | Deep server rule enforcement, intelligent quarantine protocols. | File integrity checks, automated administrative lockdown features. |
While cloud-based WAFs (like Sucuri or Cloudflare) provide excellent network-level protection, endpoint firewalls (like Wordfence) excel at understanding deep, native WordPress application logic. An endpoint firewall resides directly on the filesystem and can intelligently identify when an authenticated user is attempting privilege escalation, a nuance that a DNS-level WAF might entirely misinterpret as legitimate administrative traffic. A best-practice architectural paradigm frequently layers a Cloudflare edge WAF over a Wordfence endpoint firewall, establishing a highly resilient, dual-layered barrier.
Additionally, utilizing specialized plugins like WooCommerce Anti-Fraud or Anti Fake Orders & IP Blocker allows administrators to define complex, multi-variable risk-scoring algorithms. If a checkout attempt matches specific, high-risk profiles (e.g., utilizing a disposable email domain, exhibiting rapid typing cadence indicative of a bot, or demonstrating a geolocation mismatch with the IP address), the transaction is immediately intercepted.
The inventory lock is subsequently denied before the payment gateway is ever engaged, protecting the merchant’s payment processing standing. Services integrating with IP reputation databases (like Spamhaus or AbuseIPDB) further automate the rejection of traffic originating from known malicious hosts.
Official WooCommerce Security Standards and Best Practices
To ensure long-term architectural stability, developers must adhere strictly to the official WooCommerce security best practices and hardening guidelines. The deployment of custom extensions and themes must meet stringent automated standards to eliminate basic vulnerabilities.
-
Automated Code Auditing:
All custom PHP code must be validated against the PHP Code Sniffer (PHPCS) and SemGrep tools. These utilities identify insecure patterns, ensuring zero failure results regarding SQL injection, Cross-Site Scripting (XSS), and arbitrary file inclusions. Manual auditing via tools like OWASP ZAP or GitHub Security Scanning remains a critical secondary layer.
-
Core WordPress Hardening:
Essential infrastructural hygiene must be maintained. This includes enforcing complex, unique passwords, mandating Two-Factor Authentication (2FA) for all administrative accounts, altering the default wp_ database table prefix to prevent automated SQL injections, and ensuring strict file permission constraints.
-
Data Sanitization and Prepared Statements:
Developers must utilize WordPress’s built-in prepared statements ($wpdb->prepare) for all direct database queries, entirely neutralizing SQL injection threats. All user input must undergo rigorous validation and sanitization prior to processing.
-
Advanced Inventory Synchronization:
For merchants managing extensive catalogs, reliance on native WooCommerce inventory tracking can be augmented. Deploying advanced inventory management systems—such as ATUM Inventory Management, Smart Manager, or Veeqo—allows for multi-warehouse routing and real-time synchronization. If an inventory hoarding attack targets a specific frontend node, multi-warehouse logic can preserve backend stock allocations, ensuring fulfillment operations remain uninterrupted.
Distinguishing Malicious Hoarding from Legitimate Cart Abandonment
A critical, ongoing challenge in mitigating bot-driven denial of inventory is preventing aggressive security measures (false positives) from negatively impacting genuine human consumers. It is imperative to analytically distinguish between a malicious bot rapidly hoarding inventory and a legitimate human user who simply abandons their shopping cart due to unexpected shipping costs, friction during account creation, or natural hesitation.
The global average cart abandonment rate hovers around a massive 75%. Attempting to “solve” inventory hoarding by aggressively purging all carts after a mere two minutes will result in catastrophic revenue losses from human shoppers who require time to locate their credit cards, verify shipping details, or compare prices.
Legitimate cart abandonment is highly recoverable using strategic, marketing-focused retention plugins (e.g., Recart, CartBounty, ELEX, or FunnelKit Automations). These tools deploy targeted exit-intent popups, automated Facebook Messenger campaigns, and discount-driven email recovery sequences to re-engage the customer. Furthermore, they employ psychological triggers, utilizing scarcity marketing (e.g., low stock notifications) to incentivize checkout completion. Conversely, a programmatic bot will never respond to a cart recovery email or visually interact with an exit-intent popup.
Therefore, deep behavioral analytics must be utilized to differentiate the two phenomena. Bot hoarding is definitively characterized by impossible interaction speeds (sub-second checkout completion times from landing to POST), sequential IP rotation utilizing datacenter hosts, and massive, anomalous clusters of identical items added simultaneously to disparate carts. Human abandonment features highly erratic mouse movements, distinct pauses during form filling, and interaction with various disparate elements of the site architecture prior to abandonment. Security policies, WAF thresholds, and application rate limits must be finely tuned to aggressively target the former, while deploying recovery plugins to nurture and capture the latter.
Conclusion
The comprehensive protection of a high-volume WooCommerce infrastructure against modern DDoS campaigns, business logic exploitation, and automated bot attacks demands a rigorous, meticulously configured, multi-layered architectural approach. As threat actors increasingly abandon simplistic volumetric network attacks in favor of highly sophisticated, asymmetrical Layer 7 business logic exploitation, traditional perimeter defenses have proven demonstrably inadequate.
True resilience is achieved by proactively pushing traffic validation to the absolute network edge, utilizing global Anycast CDNs and AI-driven Web Application Firewalls capable of analyzing real-time behavioral biometrics and issuing non-interactive cryptographic challenges. At the server layer, highly tuned NGINX or Apache configurations must strictly enforce rate limiting, utilizing leaky bucket algorithms and memory zones to effectively manage burst traffic without overwhelming the underlying PHP-FPM worker pool. Finally, the WooCommerce application itself must be actively hardened through the explicit deprecation of legacy protocols like XML-RPC, the deployment of intelligent, environment-aware endpoint firewalls, the implementation of stringent session timeout logic, and the aggressive utilization of modern Store API rate-limiting features.
By seamlessly integrating edge-level mitigation, server-level traffic shaping, and application-layer behavioral analysis, e-commerce architects can successfully neutralize automated checkout abuse, eradicate financially devastating inventory hoarding, entirely prevent fraudulent card testing, and ensure uninterrupted, high-availability operational stability for legitimate consumers.