Unit 4.4
Management Policies for E-commerce Security
IT 204: E-Commerce
Today's Objectives 🎯
By the end of this chapter, you will be able to:
- ✅ Understand that technology alone is not enough to ensure security.
- ✅ Describe the purpose of a risk assessment.
- ✅ Explain the importance of a written security policy.
Beyond Technology: The Human Element
Technology provides the tools for security (firewalls, encryption, etc.).
But management policies provide the strategy and the rules for people to follow.
Effective E-commerce Security = Technology + Management Policies
The Three Pillars of Security Management
1. Risk Assessment
Identify & Prioritize Threats
2. Security Policy
Define Rules & Responsibilities
3. Auditing
Verify & Improve Compliance
These three pillars form a continuous cycle of security improvement.

Pillar 1: Risk Assessment 📊
Definition: The process of identifying, analyzing, and evaluating security risks to your organization's assets.
- Goal: Determine the likelihood and potential impact of different threats.
- Outcome: Allows you to prioritize security spending and resources effectively.
- It answers the question: "What should we be most worried about?"
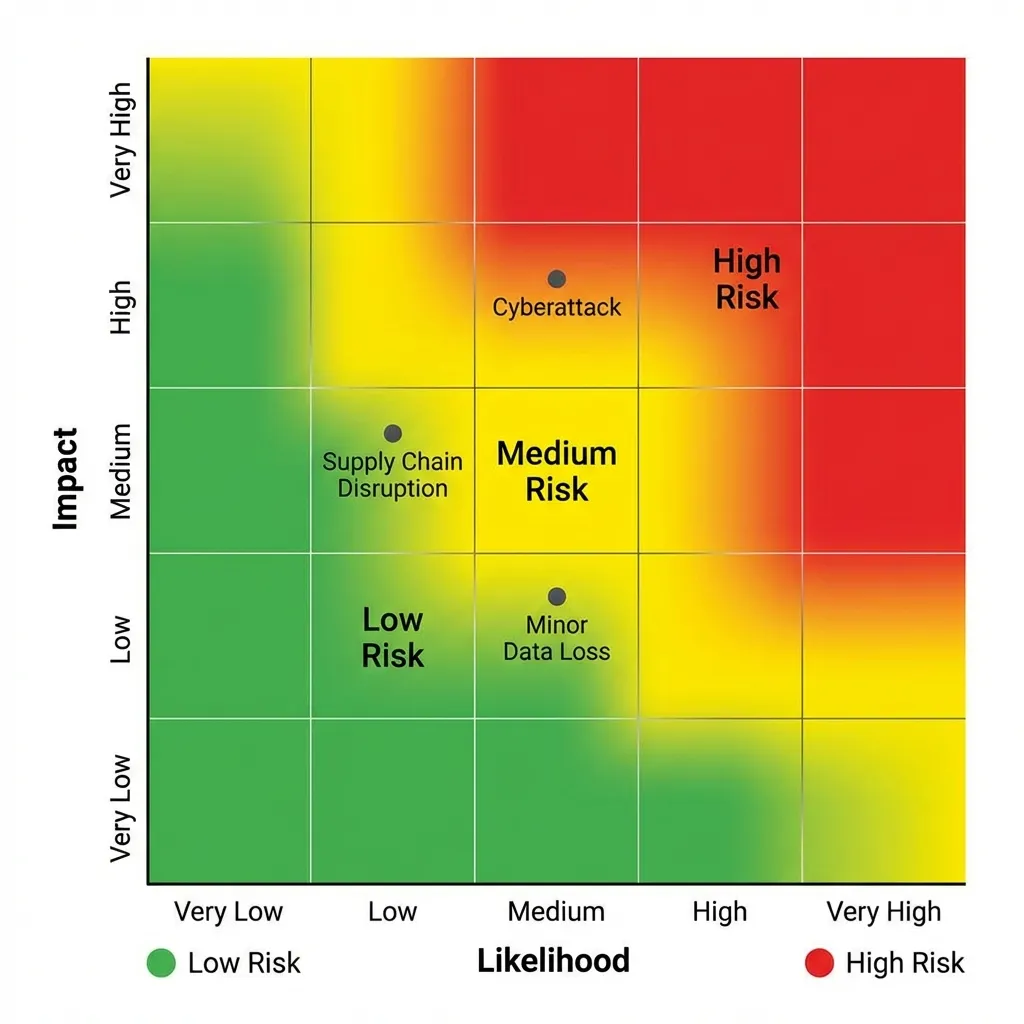
The Risk Assessment Process
- Identify Assets: What are we protecting? (e.g., customer data, payment systems, brand reputation)
- Identify Threats: What can go wrong? (e.g., hacking, malware, employee error, natural disasters)
- Analyze Risks: How likely is it, and how bad would it be? (Likelihood x Impact = Risk Level)
- Prioritize: Focus on high-likelihood, high-impact risks first.
Interactive: Risk Matrix Challenge
Select a threat below, then click the correct quadrant to place it.
Threats:
Pillar 2: The Security Policy 📜
Definition: A formal, written document that outlines the rules and procedures that must be followed to protect an organization's assets.
It defines who is responsible for security and what actions to take during a security breach.
If it's not written down, it's not a policy—it's just a suggestion.

What's Inside a Security Policy?
Core Components
- Acceptable Use Policy (AUP)
- Password Complexity & Expiration
- Data Handling & Classification
- Incident Response Plan
- Remote Access Rules
Key Questions Answered
- Who can access what data?
- How should sensitive data be stored?
- What happens if a laptop is stolen?
- What are the consequences for violations?
Interactive: Build a Security Policy
Match each policy component on the left to its correct description on the right. Click a component, then click its match.
Policy Component
Description
Pillar 3: Security Auditing 🔍
Definition: A systematic evaluation of an organization's security policies and procedures to ensure they are being followed and are effective.
- An audit is a "health check" for your security program.
- It verifies that the written policy matches real-world practices.
- Identifies gaps, non-compliance, and areas for improvement.
Interactive: Audit Finding Classifier
Read each audit finding. Click Compliant or Non-Compliant.
Practical Application: E-commerce in Nepal 🇳🇵
Scenario: A Nepali Online Marketplace
- Risk Assessment: Might identify fraud on digital wallets (eSewa, Khalti) and DDoS attacks during Dashain sales as high-priority risks.
- Security Policy: Must include a clear policy on handling customer PII (Personal Identifiable Information) to comply with Nepal's privacy laws, like the Privacy Act, 2018.
- Audit: An auditor would check if developer access to the live customer database is properly restricted and if two-factor authentication is enforced for all administrative accounts.
Interactive: Nepal E-commerce Threat Prioritizer
For a Nepali online marketplace, drag each threat to the correct priority bucket. Select a threat, then click a bucket.
Threats:
Summary & Key Takeaways ⚡
- Holistic Security: Security requires both robust technology and clear management policies.
- Risk-Informed Strategy: A risk assessment is the foundation that guides your security efforts and spending.
- Policy is Paramount: A written security policy is essential for communicating rules, defining responsibilities, and ensuring consistency.
- Continuous Improvement: Regular audits ensure policies are effective and followed, creating a cycle of security improvement.
Interactive: Three Pillars Quick Quiz
Test your understanding of this chapter. Answer all 5 questions.
Let's Discuss
Discussion Questions
- Why is a *written* security policy so much more effective than an unwritten one?
- Who should be involved in creating a company's security policy? (Hint: It's not just the IT department).
- What are some specific things a security audit might look for at an e-commerce company like Sastodeal or Daraz?
Thank You
Any questions?
Next Topic: Unit 4.5: E-commerce Payment Systems